1 min read
The 2nd Key to Unlocking a DevOps Culture: The vRad Development Pipeline
Welcome back to the vRad Technology Quest. At vRad, we value our ability to deliver frequent, regular, and minimally interruptive releases and today...

Remote radiologist jobs with flexible schedules, equitable pay, and the most advanced reading platform. Discover teleradiology at vRad.

Radiologist well-being matters. Explore how vRad takes action to prevent burnout with expert-led, confidential support through our partnership with VITAL WorkLife. Helping radiologists thrive.

Visit the vRad Blog for radiologist experiences at vRad, career resources, and more.

vRad provides radiology residents and fellows free radiology education resources for ABR boards, noon lectures, and CME.

Teleradiology services leader since 2001. See how vRad AI is helping deliver faster, higher-quality care for 50,000+ critical patients each year.

Subspecialist care for the women in your community. 48-hour screenings. 1-hour diagnostics. Comprehensive compliance and inspection support.

vRad’s stroke protocol auto-assigns stroke cases to the top of all available radiologists’ worklists, with requirements to be read next.

vRad’s unique teleradiology workflow for trauma studies delivers consistently fast turnaround times—even during periods of high volume.

vRad’s Operations Center is the central hub that ensures imaging studies and communications are handled efficiently and swiftly.

vRad is delivering faster radiology turnaround times for 40,000+ critical patients annually, using four unique strategies, including AI.
.jpg?width=1024&height=576&name=vRad-High-Quality-Patient-Care-1024x576%20(1).jpg)
vRad is developing and using AI to improve radiology quality assurance and reduce medical malpractice risk.

Now you can power your practice with the same fully integrated technology and support ecosystem we use. The vRad Platform.

Since developing and launching our first model in 2015, vRad has been at the forefront of AI in radiology.

Since 2010, vRad Radiology Education has provided high-quality radiology CME. Open to all radiologists, these 15-minute online modules are a convenient way to stay up to date on practical radiology topics.

Join vRad’s annual spring CME conference featuring top speakers and practical radiology topics.

vRad provides radiology residents and fellows free radiology education resources for ABR boards, noon lectures, and CME.

Academically oriented radiologists love practicing at vRad too. Check out the research published by vRad radiologists and team members.

Learn how vRad revolutionized radiology and has been at the forefront of innovation since 2001.

%20(2).jpg?width=1008&height=755&name=Copy%20of%20Mega%20Nav%20Images%202025%20(1008%20x%20755%20px)%20(2).jpg)

Visit the vRad blog for radiologist experiences at vRad, career resources, and more.


Explore our practice’s reading platform, breast imaging program, AI, and more. Plus, hear from vRad radiologists about what it’s like to practice at vRad.

Ready to be part of something meaningful? Explore team member careers at vRad.
3 min read
 Brian (Bobby) Baker
:
August 31, 2017
Brian (Bobby) Baker
:
August 31, 2017

Welcome once again to the vRad Technology Quest series – let's dive in.
Cyber Security is a hot topic. The frequency of notable events – ranging from the compromise of large corporations to possible state-sponsored security breaches – is increasing.
Security has become particularly important in health care: research suggests that patient information is now more valuable than credit card numbers for fraud and cyber security is the frontline defense in protecting health care companies.
vRad’s proactive approach to cyber security falls into multiple buckets – user training, network security, email security, application security and many more.
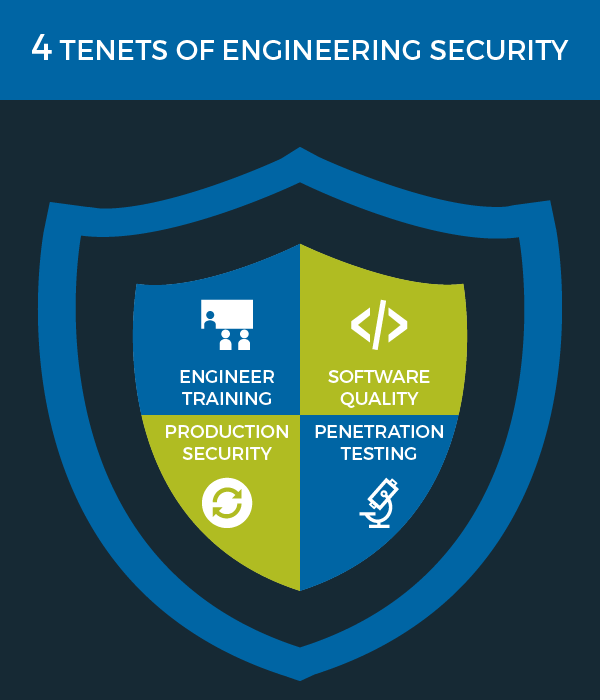
For my part, I’ll share some specifics about our application security and its integral role in our overall approach to developing software. I break Engineering's approach to security into four tenets:
Let’s take a look!
First and foremost, we make sure our team of engineers has the tools and training they need to stay up-to-date on best practices.
One core aspect of this training is security, with a focus on web application security. vRad places a high value on enabling our engineers by providing the training they need to be successful; the more we can educate ourselves about potential flaws and common problems, the better we can find and avoid pitfalls in our code base. We often refer back to the Open Web Application Security Project (OWASP) Top 10.
Our security training comes in a wide range of mediums including internal seminars, usage of our training platform Pluralsight, and white papers. Greg, our security manager at vRad, is a huge help in delivering corporate-wide training as well as engineer-targeted training to help us stay on track. We also focus on finding and sharing content among engineers and holding lunch-and-learn sessions.
Software Quality is the largest component of our security efforts; we believe that quality and security go hand-in-hand and we work hard to incorporate quality every step of the way, from idea to production. Some of this may seem pretty obvious, yet must not be overlooked:
We tie security and quality together tightly – our quality processes are security practices, too. This helps to ensure that we are always thinking about security, that multiple people are asking the question “is this secure?” and that we’re adding testing that validates security measures we put in place.
Our production environments are monitored closely from multiple angles - one of which is security. I mentioned above that reviewing and testing code base enhances our quality process. One of the ways we ensure this is through internal auditing – much of which is automated.
In a similar fashion, we monitor all changes to production. Each alteration to production applications is carefully monitored and tracked. Engineers review each change and ensure that it was expected – or rather, it tracks back to our change management tool – and that the person who made the change was authorized to be making those changes.
We also monitor the groups who have access to make changes. vRad operates 24x7x365 and emergencies happen; engineers get called in and need special permissions in the environment to perform necessary adjustments. We are careful to track and audit these occurrences on a routine basis to ensure that only the appropriate people have permission. We strive for a fine balance between enabling people to keep the platform operating smoothly and avoiding unnecessary risk of having too many folks with too much access.
I saved the best topic for last.
 |
Penetration Testing is a simulated attack on a system to determine if security vulnerabilities are present. |
vRad performs multiple types of penetration tests on our systems.
First, we have external organizations perform penetration testing – we provide them with a basic understanding of our applications and a development environment and let them try to break into our systems. This provides a great objective perspective of our application security.
Second, we perform internal penetration testing. Our security models tend to be layered; we don’t expect anyone to be able to get around the first layer, but if they do, we have secondary security measures in place. Because of this, we conduct additional “white box” testing – we design tests and setup scenarios in which the first layer of security has been compromised to validate the secondary measures are successful. A significant number of these tests are automated (see my earlier post on Test Automation (4)), so they run at least nightly and often more frequently on our code base.
These four focus areas help us secure our applications and are instrumental in keeping our patients’ and clients’ information safe.
Thanks for joining me on the second to last leg of our technology quest. I hope you join us for our final topic on maintenance and release windows (#7) – the ultimate aspect of our ability to deliver patient care 24x7x365. And remember, you can always catch up on any DevOps Keys you may have missed in the vRad Technology Quest Log.
Until Next Time,
Brian (Bobby) Baker

1 min read
Welcome back to the vRad Technology Quest. At vRad, we value our ability to deliver frequent, regular, and minimally interruptive releases and today...

1 min read
At vRad, we have a passion for connecting – with each other, with clients, and with patients. In technology, we strive to break down the language...

1 min read
vRad’s philosophy around frequently deploying software updates relies heavily on test automation, which ensures adequate test coverage for each...
vRad (Virtual Radiologic) is a national radiology practice combining clinical excellence with cutting-edge technology development. Each year, we bring exceptional radiology care to millions of patients and empower healthcare providers with technology-driven solutions.
Non-Clinical Inquiries (Total Free):
800.737.0610
Outside U.S.:
011.1.952.595.1111
3600 Minnesota Drive, Suite 800
Edina, MN 55435